DGND3700 V1 Transmission Firmware
This page contains all the custom firmware files for Netgear's DGND3700 V1 / N600 (ADSL/VDSL(FTTC)/WAN Router).
(The DGND3700 V2 is a different Broadcom chipset and only supports ADSL, NOT VDSL!)
- NOTE this is built based upon Netgear's released GPL source code and is not related in any way to Netgear beyond that.
Contents
- 1 Added Features
- 2 Updated Features
- 3 DOWNLOAD Multi DGND3700v1/3800 GENIE Firmware
- 3.1 Latest 2018-03-11
- 3.2 2017-10-06
- 3.3 Firmware discussion forum
- 3.4 Previous Releases
- 3.5 2017-05-17
- 3.6 2017-05-15
- 3.7 2016-12-17
- 3.8 Changelog 2016-12-17
- 3.9 Changelog 2016-12-10
- 3.10 Changelog 2016-04-10
- 3.11 Changelog 2015-12-04
- 3.12 Changelog 2015-11-09
- 3.13 Changelog 2015-10-30, BETA2
- 3.14 Changelog 2015-05-21, BETA1
- 3.15 Previous Releases
- 4 See Also
- 5 Notes/FAQ/Help/Instructions/Manual - Original Firmware
- 5.1 Network Services
- 5.2 Cron
- 5.3 Dropbear (SSH/SFTP)
- 5.4 DNS (DNSMasq)
- 5.5 Port forwarding
- 5.6 Modifying firmware behaviour on the fly
- 5.7 OpenVPN
- 5.8 Telnet daemon
- 5.9 L2 Bridge
- 5.10 Transmission
- 5.11 Automatic
- 5.12 ADLS/VDSL
- 5.13 Inadyn-mt (DynDNS)
- 5.14 Ethernet WAN port to LAN
- 5.15 SSH / SFTP / Dropbear
- 5.16 PXE Booting
- 6 Building your own version
- 7 Comments
Added Features
- Avahi (Bonjour) network discovery for most services
- Transmission (Bittorrent) [including relevant network tweaks to tcp_fin_timeout/tcp_keepalive_time/rmem_max/wmem_max ]
- Automatic torrent RSS feeder
- Full ADSL Mode Setting, ADSL/VDSL , Target SNR Margin (10% increments), PhyRexMt
- Inadyn-mt Dynamic DNS Support
- e2fsprogs Format/check ext2/3/4 filesystems directly on device
- Large files support to filesystem limits
- Add 5th LAN port by reassigning ethernet WAN port to the bridge (eth0 to br0)
- NFS 2,3 and 4
- Filesystem, EXT 2,3 (& 4 as experimental in kernel), HFS+ r/o
- Dropbear SSH with sftp-server (OpenSSH), LAN and WAN access.
- strace for developers
- DNSMasq DHCP / DNS caching and PXE booting
- p910nd non-caching print server daemon (hotplug started)
- Lots more Busybox programs enabled.
- Crontab/crond (time based job scheduler)
- SNMP daemon
- RIP re-enabled (zebra ripd)
- OpenVPN
- Wake-On-Lan (send magic packet to wake LAN machine)
- Ad-blocking via DNS (using DNSMasq with http://pgl.yoyo.org/adservers/ blocklist)
- WAN VLAN tag ID (for certain VDSL providers such as BT Infinity)
- IGMP Proxy - (for IPTV [with VDSL services], modified with wl-500 oleg patches for 0.0.0.0/1 altnet)
- bbe binary block editor (dev use, alter the propietry binaries)
- TCPdump realtime network log/monitor
- iperf3 network performance analyzer
- LiME kernel memory dumper
Updated Features
- ADSL/VDSL firmware replaced with latest PHY A2pv6C039t.d23k
- ADSL/VDSL granular mode selection, granular options selectable.
- miniDLNA (ReadyShare) Supports more TV's and devices & now works properly daemonized.
- Samba 3.6 (Support SMB2, years of bugfixes & improvements.)
- NTFS-3G 2014 (many fixes, improved Windows 8 NTFS compatability)
- udhcpd replaced with DNSMasq (works properly, faster, more features, DNS attack protection, caching, Ad-blocking, PXE Boot)
- Automounting USB via disk Label, falling back to UUID, then block device number.
- USB drive using spinning media CFQ I/O scheduler, (not NOOP!)
- Priority of all non-vital programs lowered to stop router hanging/crashing on CPU load.
- Time set from from time.nist.gov and pool.ntp.org on WAN up rather than Netgear's (sometimes problematic) time servers.
DOWNLOAD Multi DGND3700v1/3800 GENIE Firmware
Latest 2018-03-11
- Added (much) newer B2pvC038v DSL phy for Annex B
- Updated Transmission, openSSH, miniDLNA(ReadyShare), zlib
2017-10-06
- Updated DNSmasq to 2.78 (recent security vulnerability fixes)
- Updated openSSH 7.5p1
- Updated openSSL 1.0.2l
- Updated BusyBox 1.27.2 (+ fixed incorrect df disk space size reporting, thanks Jewelie.)
Known issues:
- DHCP Extra Options doesn't work. For Sky Fibre you will need the Legacy firmware version
aka non-genie firmware, https://www.richud.com/wiki/DGND3700_V1_Transmission_Firmware_Legacy
- Vodafone Italia VDSL doesn't work. Use release Genie 2017-05-15 instead. (below)
Firmware discussion forum
- External link to Netgear discussion forum about the modded firmware
The latest build of the next firmware is linked on the Netgear forum thread above, it is based on the 3800 'Genie' firmware with revised interface. It supports DGND 3700V1/3800, both Annex A & B. For Annex A it has the latest ADSL PHY supporting G.INP [verified working] & Vectoring [SRA and G.INP need enabling]
Previous Releases
2017-05-17
As release on 15th (below) minus the problematic PPPoE host-uniq mod for Vodafone Italia VDSL
Known issues: DHCP Extra Options doesn't work. For Sky Fibre you will need the Legacy firmware version
2017-05-15
- - pulled due to reported problems with PPPoE connections on other ISPs -
use ONLY if you need extra host uniq options for Vodafone Italia VDSL.
Changelog
- Working on all 3800 models (hopefully).
- hostname assigning with DHCP fixed
- adblock white/blacklist character limit increased
- NTP timezone sets all system time properly.
- PPPoE modified to add host uniq feature setting. (see above)
- minor fixes and updates of software
2016-12-17
Changelog 2016-12-17
- DSL firmware bumped to A2pv6C039t (Thanks to Bukchoi for blob)
- NVRAM default Idle Timeout set to 0 (unlimited)
- Dropbear updated 2016.73 > 2016.74
Changelog 2016-12-10
Fixes
- Resetting now ends up with Genie interface in English and no German connection setup wizard! (Thanks to Burt's kind spare router donation)
- A few minor mistakes with the default config seeding fixed.
- Backported Google's TCP CUBIC fix to kernel
Updates
- ADSL PHY > A2pv6C039r.bin (Thanks to Bukchoi for blob)
- busybox > 1.25.1, (added flash_eraseall)
- dnsmasq > 2.76
- p910nd > 0.97
- openSSL > 1.0.2j
- e2fsprogs > 1.43.3
Changes
- Adblocking - now can pick multiple block lists, add a custom list, blacklist and/or whitelist specific domains. (Also altered how this works slightly so a blocked domain returns NXDOMAIN rather than resolving locally, making it fractionally faster.)
- Mounting a FAT volume is now defaulted to shortname=mixed, as per more recent kernels.
Changelog 2016-04-10
Updates
- Avahi, NFS utils, libxml, openSSL, NTFS-3g, Dropbear, Sqlite, Transmission, Busybox, openVPN
Fixes
- openVPN should now work. .ovpn generator added.
- Lots of minor fixes. (Including input sanitizing on textarea boxes that I messed up!)
- Re-enabled functionality of www.routerlogin.com www.routerlogin.net to get to interface.
Additions
- HPN-ssh (Pittsburgh Supercomputing Centre) patches for faster SCP
- Re-enabled Wifi DFS channels.
- NTP now has its own config page.
- Help files (man pages mostly) now done
- Transmission has new option to update blocklist on program startup.
Known Issues
- mke2fs hangs for reasons unknown, if you need to format your external drive you will have to plug it into a regular PC.
- Some settings are stored differently so will need re-adding on new firmware if updating from old [non-GENIE].
Changelog 2015-12-04
- Fixed PF (port forwarding) issue by using alternate NVRAM values.
- Fixed Samba sharing free space problem.
- Removed duplicate time zone (TZ) entries
- Updated miniDLNA 1.1.3 > 1.1.4, samba
- Re-enabled allowing duplicate SSID for 2.4GHz and 5GHz
Changelog 2015-11-09
- Decided to make it no longer BETA.
- Source from 3.0.0.16 to 3.0.0.22 [aka 3.1.22]
- Updated dnsmasq 2.72, busybox 1.24.1, dropbear-2015.68, openssl 1.0.2d
- Fixed 2.4GHz wifi not coming up on boot for some people
- Rejigged web GUI interface a bit fixing some layout problems, adding some more bits.
Changelog 2015-10-30, BETA2
- Updated Inadyan-mt v02.24.47, minidlna-1.1.5 and various other programs
- Fixed memory leak in web interface code
- Fixed tons of other minor things
- Added extra config options to various program interfaces in web GUI
Changelog 2015-05-21, BETA1
- First beta release, brand new ADSL PHY!
- Proper port mapping/triggering
- AJAX web interface (on new/added bits)
Previous Releases
2016-12-10 DGND3x00_2016-12-10
2016-04-10 DGND3x00_2016-04-10
Second Release 2015-12-04 DGND3x00_2015-12-04
First Release 2015-11-09 DGND3x00_2015-11-09_18:28.tar.xz
Second BETA release 2015-10-30 DGND3x00_2015-10-30_22:35.tar.xz
First BETA release 2015-05-21 DGND3x00_2015-05-21_20:49.tar.xz
See Also
Notes/FAQ/Help/Instructions/Manual - Original Firmware
I am afraid this an an eclectic mix of info at the moment.
- Please note everything below applies to the old non-GENIE firmware so may or not be relevant to new.
Network Services
- You can only use start/stop when the service is enabled only.
Cron
This will let you 'do something' on a time schedule. Cron Info
Turn wireless on/off
- 2Ghz = 'wla_' = wl0
- 5Ghz = 'wlg_' = wl1
Turn OFF both 2 & 5Ghz daily at 23:15, crontab entry is
15 23 * * * param set wla_wlanstate=Disable;param set wlg_wlanstate=Disable;pkill -SIGUSR1 wlanconfigd
Turn ON both 2 & 5Ghz daily at 06:15, crontab entry is
15 6 * * * param set wla_wlanstate=Enable;param set wlg_wlanstate=Enable;pkill -SIGUSR1 wlanconfigd
If for example you already have 5Ghz disabled, omit the wlg_ part from both entries (semi colon separates commands)
- Example
/tmp/var/log # crontab -l 15 23 * * * param set wla_wlanstate=Disable;param set wlg_wlanstate=Disable;pkill -SIGUSR1 wlanconfigd 20 6 * * * param set wla_wlanstate=Enable;param set wlg_wlanstate=Enable;pkill -SIGUSR1 wlanconfigd 00 22 * * * /etc/init.d/transmission.sh stop;/etc/init.d/automatic.sh stop 00 09 * * * /etc/init.d/transmission.sh restart;/etc/init.d/automatic.sh restart
Dropbear (SSH/SFTP)
l:admin p:<same as routers web page>
- When the ADSL/ppp comes up, dropbear's connection will drop, you will probably only notice this if you connect while its still in final stages of booting up
Can enable or disable firewall to allow WAN access (setting: 'SSH/SFTP WAN Access')
Very strongly suggest you set a complex password if you are enabling external SSH access! Bear in mind you can tunnel almost anything through SSH to any machine on your LAN
DNS (DNSMasq)
DHCP, DNS, PXE boot (wired), Ad-blocking are all provided by DNSmasq.
A third DNS server can be set via Network Settings page, which appends to ISP assigned ones.'All Servers' feature is enabled so it will pick the result from the fastest server to respond. This is useful if your ISP's servers are not always reliable.
Ad-blocking
At the time of writing this is just enabled or disabled as a network service (can specify your own via NVRAM variable assuming in correct format). The Blocklist is from http://pgl.yoyo.org/adservers/ which has been going for over a decade with regular updates. It is a fairly small list of ~2500 address yet will block 99% of ads and not have any performance impact on general DNS resolution. As it runs at the DNS resolution level ad's cannot be obfusticated in Javascript or Flash etc. See here for ad-filtering info
- The list must be in dnsmasq format
- The list specified will get processed to change 127.0.0.1 to 0.0.0.0
- The process: WAN connection comes up > latest list downloaded > DNSmasq restarted. Any domain in the list will then redirect to IP 0.0.0.0, effectively blocking it.)
- Most of the time the blocking goes unnoticed, I find when I am at work with no blocking I DO notice lots more ads everywhere.
The only known issues are ;
- In a tiny minority of web sites, the ad display area is hard-sized and you may get a grey box saying it can't be found (eBay for example).
- If you follow a web link that hops through an advert site (AdFly) or redirects (a google 'Ad') then it won't work. Very unlikely to happen on 'normal' web sites!
Port forwarding
The web UI only lets you map incoming connections on the WAN to the same internal port.
If you want to map to different ports you need to do it with a uPnP client (using UPnP-IGD protocol).
In a Linux based OS such as Ubuntu, 'uPnP Router Control' will do it.
Modifying firmware behaviour on the fly
These are for the mode advanced user.
Script Hooks
rcS (startup), wan-pre.sh and wan-up.sh have several hooks in them, these basically evaluate a nvram parameter, i.e. execute the contents.
e.g. Manipulating QoS, this will get executed at the end up wan-up, when the WAN connection comes up (via PPP in this case).
For a 512 kbit upload sync connection on pppoa, this will help stop upload slowdown. Thanks to Ali1234 for the tip. See Section 9.2.2.2 here, tc docs
param set wanup_hook_2="tc qdisc replace dev pppoa0 root tbf rate 500kbit latency 50ms burst 1540" param save
- On VDSL (2MBit up 40Mbit down) I use this, atm0.101 is VDSL interface on VLAN ID 101
param set wanup_hook_2="tc qdisc replace dev atm0.101 root tbf rate 1900kbit latency 50ms burst 1740" param save
Config Hooks
(requester: G. Ashman)
Dnsmasq has a config file hook at the end of the config file.
Adding anything into this nvram parameter 'dnsmasq_custom_options' will append to the end of the configuration. Any duplicate directives should get replaced.
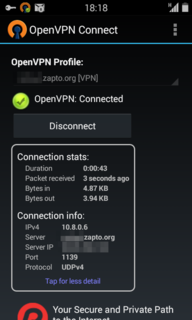
OpenVPN
- This is designed to 'just work'. Enable it on DGND3700, (securely) download the 4 generated keys, setup your client with these 4 keys.
- openVPN by default now generates/uses TLS rather than static keys. The following instructions now apply to build 2014-10-26 and above.
ONLY If you were using 2014-10-26 , clear the nvram setting for it to start up and build new TLS keys and settings, telnet/ssh in and do;
param unset openvpn_value param save reboot
Enable 'OpenVPN server' in 'Network Services', then start it, or reboot.
When the service starts for the first time it will set randomly generated unique security key(s) and some defaults. (This is why it takes a while to start, 400Mhz CPU !)
Get new TLS keys
Then SFTP into the router, with Filezilla for example, and get the following certificates.
/tmp/CA/client1.pem (User Certificate) [User's public certificate] /tmp/CA/client1.key (Private Key) [User's private certificate] /tmp/CA/ca.pem (CA Certificate) [CA's public certificate] /tmp/CA/hmac.key (Additional authentication > key file, no key direction) [HMAC key]
To connect to the VPN / Install client software
Ubuntu get the network manager plugin, "sudo apt-get install network-manager-openvpn", go to Network manager > VPN Connections > Configure VPN, Add > VPN > OpenVPN (note it wont be there until you install plugin first).
OpenVPN client config
There are 4 certificates to setup.
These are the DEFAULTS you would set on the CLIENT, see below on changing them.
Under the VPN Tab
General
Gateway: <You Routers external IP>
Authentication
Type : Certificate (TLS)
User Certificate: client1.pem
CA Certificate: ca.pem
Private Key: client1.key
Private Key Password: <leave blank>
Advanced
General Tab - If you change the default port you alter it here
TLS Authentication Tab
Tick 'Use additional TLS authentication
Key File: hmac.key
Key direction: <leave blank>
- Leave everything else default....
NVRAM values used
port ='openvpn_port', main config 'openvpn_value', keys are stored with their name as xxxxxxxx , e.g. openvpn_xxxxxxxx
Changing openVPN settings
Most configuration options with openVPN are quite advanced, the only thing anyone is likely to need to alter is the port and is avialalbe on web interface. For everything else, just set the 'openvpn_value' key, then 'pkill -HUP openvpn' to restart it. Remember to quote the string with double quotes, e.g. param set openvpn_value="<your config here>".
If you want to change to the more complicated key setups, suggest storing them in /tmp/mnt/storage or your attached USB device.
Reset it if you break it
If you mess about and break everything, do this to reset it all (it will regenerate with defaults), i.e. reset port, reset configuration, reset all the certificates.
param unset openvpn_port param unset openvpn_value /etc/init.d/openvpn.sh cleancerts param save reboot
- Note, this router does not use/support iptables so using openVPN to connect out (rather than connecting in, as above) may not be possible how you want to do it.
OpenVPN on Android
If you are using Ubuntu you can export the VPN settings (.conf) from Network Manager and rename it (.ovpn) , then import it into Android.
Copy the 4 keys you download from the router /tmp/CA folder and the conf file (.ovpn) to a folder on the SD card (e.g. /VPN/ ).
Then just import the .ovpn in the openVPN app in Android.
The .ovpn should look something like this, the only thing you will need to change is the 'remote' bit.
In this example I am using xxxxxxx.zapato.org as my routers hostname (using no-ip.org), and non standard port 1139.
--------------------------------------------- client remote xxxxxxx.zapto.org 1139 ca ca.pem cert client1.pem key client1.key dev tun proto udp tls-auth hmac.key nobind auth-nocache script-security 2 persist-key persist-tun user nobody group nogroup ----------------------------------------------
Telnet daemon
Allows opening a terminal without needing any login credentials (therefore there is obviously no WAN access)
L2 Bridge
Info kindly sent from Stephen Ashley
mod to make it a Plain L2 Bridge with the ADSL/VDSL port in the same bridge group as the 4 switch ports
- 1/ Turn off both WiFi radios.
- 2/ Enable ssh
- 3/ Login to rtr and add following :-
param set rcS_hook_3="/bin/brctl delif br0 wl1; /bin/brctl delif br0 wl0; /bin/brctl addif br0 atm0" param save
- 4/ Save / update router, reboot.
Once rebooted login again and check that Hook 3 param is working, you should see some same as this ;
~ # /bin/brctl show
bridge name bridge id STP enabled interfaces
br0 8000.841b5e46e765 no eth1
eth2
eth3
eth4
atm0
~ #
- 5/ Your now good to connect the ADSL/VSDL port and your Router/PC to ONE (only) of the 4 switch ports and run PPPoE on that router etc.
Transmission
To use transmission you need (very) preferably an EXT3 formatted drive*, with a folder in the root created called 'transmissionbt'.
Starting the service without this will have no effect. [This ensures the router wont write default configurations and files to everything plugged in unintentionally when automounting.]
Security options can be changed from the Netgear web interface, all other options can be changed via Transmission's own webGUI - but you need to stop transmission from Netgear web interface to make it save settings (it saves on program exit only, cannot force a save via its own web interface sadly.)
- The performance of NTFS is terrible due to high CPU usage, please don't use NTFS formatted drives if at all possible.
Strongly suggest setting any external access IP's in the RPC whitelist and setting an RPC password
Automatic
Monitors RSS feeds then filters and drop/start torrents automagically.
It requires one or more RSS feeds and one or more filters (that apply to all feeds). Optionally a target folder can be specified for each filter.
Filtering requires some basic understanding regular expression matching, PCRE syntax for detailed filtering.
e.g. Sample RSS Feed URL
http://rss.thepiratebay.se/205
e.g. Sample Filter (basic), Episodes 01 to 09 of season 01
Beware.the.Batman.S01E1[0-9].*1080p.WEB-DL.*
- Note all the filters apply to all the feeds, (Automatic does have the ability to tie them together however this would make the web interface too complicated, imho.)
ADLS/VDSL
The router supports (thanks to Malcolm Rowe's explanations here );
- IPoEoATM: (DSL (ATM (AAL5 (RFC 2684 bridged (Ethernet (IP)))))) [aka RFC 1483 Bridged]
- PPPoE: (DSL (ATM (AAL5 (RFC 2684 bridged (Ethernet (PPPoE (PPP (IP))))))))
- IPoA: (DSL (ATM (AAL5 (RFC 2684 routed (IP)))))
- PPPoA: (DSL (ATM (AAL5 (RFC 2684 routed (PPP (IP))))))
with MER & VLAN ID
Can fine tune most DSL line mode settings on Advanced interface.
VDSL2 (FTTC)
Please submit you WORKING settings to help others
Some common VDSL/Fiber (FTTC) ISP settings (reported to me as working) :
| Country | ISP(s) | Multiplexing (AAL5) | VPI** | VCI** | Transfer Mode | WAN VLAN ID | Protocol | Login | Pass | DHCP Additional (MER) | Verified by |
| Australia | TransACT | LLC | 8 | 35 | PTM | 10 | PPPoE | >from ISP< | >from ISP< | Ron3KL | |
| USA | CenturyLink (old Qwest region) | VC | 0 | 38 | PTM | 201 | PPPoE | >from ISP< | >from ISP< | w3wilkes | |
| UK | EE Fibre | VC | 0 | 38 | PTM | 101 | PPPoE | xxxx.orangehome.co.uk@fs | >from ISP< | whskerp | |
| UK | BT Infinity | VC | 0 | 38 | PTM | 101 | PPPoE | bthomehub@btbroadband.com | >blank< | mosi4 | |
| UK | Shell Energy | VC | 0 | 38 | PTM | 101 | PPPoE | username@first-utility.com | password | richud | |
| UK | TalkTalk Fibre | LLC | 0 | 38 | PTM | 101 | IpoEoATM | richud | |||
| UK | Sky Fibre/NOW TV (see notes) | LLC | 0 | 38 | PTM | 101 | IpoEoATM | Option 61 encoding login/pass* | burt35/richud | ||
| Poland | Orange Neostrada Fiber | LLC | 0 | 35 | PTM | 35 | PPPoE | >from ISP< | >from ISP< | hagnar | |
| Italy | Fastweb Fibra | LLC | 8 | 36 | PTM | IpoEoATM | pdneri | ||||
| Italy | Fastweb Fibra Ultra | LLC | 1 | 32 | PTM | IpoEoATM | mauri_va, (clone MAC) | ||||
| Italy | Telecom Italia Smart Fibra | LLC | 8 | 35 | PTM | 835 | PPPoE | Antonio bruno | |||
| Italy | Vodafone Italia FTTC | LLC | 8? | 35? | PTM | 1036 | PPPoE | vodafoneadsl | vodafoneadsl | Antonio bruno | |
| Greece | Ote and HOL | LLC | 0 | 35 | PTM | 835 | PPPoE | >from ISP< | >from ISP< | Dimitrios T. |
- ∗ DHCP extra option 61 (-x 0x3d:) setting your formatted username/password combination
username@skydsl|passwordconverted to a hex string. e.g. set 'DHCP Client Extra Options' set-x 0x3d:757365726e616d6540736b7964736c7c70617373776f7264,
(everything highlighted, i.e including the -x 0x3d: prefix followed by hex string)
- DHCP Extra Options (Option 61) doesn't work on latest GENIE firmware. You will need the most recent Legacy firmware version
aka non-genie firmware, https://www.richud.com/wiki/DGND3700_V1_Transmission_Firmware_Legacy
- UPDATE Sept/2022 - works on this firmware verified with NOW TV fibre, login/pass doesn't seem to matter (abcdefghi@skydsllqwertyuio), i.e. just set -x 0x3d:61626364656667686940736b7964736c6c71776572747975696f
(can aslo set from CLI ~ # param set system_name_0="-x 0x3d:61626364656667686940736b7964736c6c71776572747975696f"
To test you should see in ps, showing ... dhcpc -i atm0.101 -p /var/run/udhcpc0.pid -s /tmp/udhcpc -S -x 0x3d:61626364656667686940736b7964736c6c71776572747975696f
- ∗∗ Note, VCI/VPI shouldn't be needed for VDSL2, I am just including what information has been passed to me/what the router defaulted to as provided by the ISP.
Sample VDSL2 Output log (10/100Mbit)
Inadyn-mt (DynDNS)
Please look at the man page before fiddling with the advanced options!
Ethernet WAN port to LAN
This sets the ethernet WAN port (actually eth0) to be part of the WiFi/LAN bridge device (br0), thus becoming a 5th ethernet port on the LAN.
- Note, you may also need to change 'WAN Setup' > 'WAN Preference', 'Must use DSL WAN', depending on what your connection type is.
- Note, this port will not be able to 'see' the other ethernet ports and vice versa. It will see wifi network and internet (WAN) fine. (I believe the is due to a port VLAN setting in the switch, if anyone figures out how to change it please let me know!)
SSH / SFTP / Dropbear
(SSH) Secure shell and SFTP access, both encrypted. (DSS is disabled)
SFTP gives you FTP like access securely via an SSH connection.
Access web GUI securely from WAN via SSH tunnel
- Router LAN IP : 192.168.0.1
- Router WAN IP or no-ip name : joeblow.no-ip.com
- Arbitary / unused random port on your local machine : 18000
ssh -L 18000:192.168.0.1:80 admin@joeblow.no-ip.com
This will open a terminal session and make the routers web GUI accessible locally http://127.0.0.1:18000
RDP to a machine on your LAN externally via SSH tunnel
- (RDP) PC LAN 102.168.0.15
- Router WAN IP or no-ip name : joeblow.no-ip.com
- Arbitary / unused random port on your local machine : 18000
TBC
PXE Booting
The router has built in PXE boot using Dnsmasq's built in TFTP server to push out ldlinux.0 (Syslinux 6.x). This then boots the menu (default) from the built web server via HTTP with Memtest86 and Memtest86+.
If you create a folder on the root of your USB drive called 'pxe', it will PXE boot from here instead. It checks for the presence of the folder and the boot config file 'default'. i.e. pxe/default. You then have complete control over what it boots. The easiest way to get this working is copy the contents of /usr/pxe from the router to pxe/ on your USB drive (probably via SFTP (Filezilla).
- Note if you have logged into the web interface on another machine and its not logged/timed out, PXE boot will fail. (ldlinux.c32 not found)
Building your own version
You need to visit DGND3700 V1 Transmission Firmware Build for details of how to make/compile it yourself. Included here is a bundle of all (my) build parts, links to external source files for new/replacement programs, the working(fixed) toolchain and link to the original N600 / DGND3700 Netgear GPL source. If you can get all the files, all you need to do is literally run 'go.sh' to rebuild it all.
Comments
blog comments powered by Disqus